The BYOD Security Market is expected to register a CAGR of 14.5% from 2025 to 2031, with a market size expanding from US$ XX million in 2024 to US$ XX Million by 2031.
The report is segmented by Device Type (Laptop, Smartphone, Tablet); Solution (Mobile Device Management (MDM), Mobile Application Management (MAM), Mobile Content Management (MCM), Mobile Identity Management (MIM)); Software (Mobile Data Security, Mobile Device Security, Network Security); Enterprise Size (Small and Medium-Size Enterprises, Large Enterprises). The global analysis is further broken-down at regional level and major countries. The report offers the value in USD for the above analysis and segments
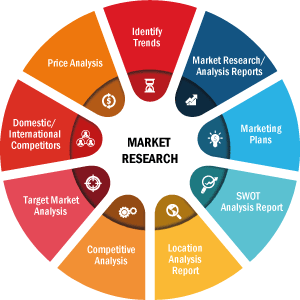
Purpose of the ReportThe report BYOD Security Market by The Insight Partners aims to describe the present landscape and future growth, top driving factors, challenges, and opportunities. This will provide insights to various business stakeholders, such as:
- Technology Providers/Manufacturers: To understand the evolving market dynamics and know the potential growth opportunities, enabling them to make informed strategic decisions.
- Investors: To conduct a comprehensive trend analysis regarding the market growth rate, market financial projections, and opportunities that exist across the value chain.
- Regulatory bodies: To regulate policies and police activities in the market with the aim of minimizing abuse, preserving investor trust and confidence, and upholding the integrity and stability of the market.
BYOD Security Market Segmentation
Device Type- Laptop
- Smartphone
- Tablet
- Mobile Device Management
- Mobile Application Management
- Mobile Content Management
- Mobile Identity Management
- Mobile Data Security
- Mobile Device Security
- Network Security
- Small and Medium-Size Enterprises
- Large Enterprises
Strategic Insights
BYOD Security Market Growth Drivers- Increase in Mobile Device Usage Increases the Demand for BYOD: The proliferation of mobile devices in the workplace has significantly driven the BYOD (Bring Your Own Device) security market. As employees increasingly use personal devices for work purposes, organizations face heightened security risks related to data breaches and unauthorized access. This trend necessitates robust security measures to protect sensitive corporate data accessed through personal devices. Businesses are investing in BYOD security solutions to ensure that they can maintain control over their data while allowing employees the flexibility of using their devices. The need for comprehensive security strategies to mitigate risks associated with BYOD is propelling market growth.
- Growing Cybersecurity Threats: The escalating frequency and sophistication of cyberattacks are compelling organizations to prioritize BYOD security. As personal devices often lack the same level of security as corporate systems, they can become vulnerable entry points for cybercriminals. Breaches can lead to significant financial losses, reputational damage, and legal ramifications. Consequently, organizations are implementing stringent BYOD security policies and investing in advanced security tools such as mobile device management (MDM) and endpoint security solutions. The urgent need to counteract emerging cybersecurity threats is a significant driver for the BYOD security market.
- Regulatory Compliance Requirements Regarding the Data Protection and Privacy: Increasing regulatory requirements regarding data protection and privacy are also driving the BYOD security market. Organizations must comply with various regulations, such as GDPR and HIPAA, which mandate stringent security measures for handling sensitive data. Non-compliance can result in hefty fines and legal consequences. As a result, companies are compelled to establish robust BYOD security frameworks that protect sensitive information while enabling employees to use their devices. The necessity to adhere to compliance standards is a critical factor fueling the demand for BYOD security solutions.
- Shift Towards Zero Trust Security Models: A significant trend in the BYOD security market is the shift towards zero trust security models. Traditionally, organizations operated on the assumption that devices within their network were trustworthy. However, the increasing use of personal devices has shifted this paradigm. Zero trust models require verification for every device, user, and network request, regardless of their location. This approach enhances security by minimizing potential attack vectors and ensuring that only authenticated users can access sensitive information. As organizations adopt zero trust principles, the demand for corresponding BYOD security solutions will continue to grow.
- Integration of IoT Devices in BYOD Policies: The rise of Internet of Things (IoT) devices in workplaces is shaping the BYOD security landscape. These devices often connect to corporate networks and can pose additional security risks if not properly managed. Organizations are increasingly recognizing the need to incorporate IoT device security into their BYOD policies, addressing vulnerabilities associated with these devices. This trend is leading to the development of comprehensive security frameworks that encompass both personal devices and IoT technology. As businesses strive to secure all endpoints within their networks, the BYOD security market will likely evolve to include IoT-specific solutions and strategies.
- Development of Advanced Security Solutions: The BYOD security market presents opportunities for the development of innovative security solutions tailored to the unique challenges posed by personal devices. Emerging technologies such as artificial intelligence (AI) and machine learning can enhance threat detection and response capabilities, providing organizations with proactive security measures. Additionally, solutions that integrate behavioral analytics can help identify anomalies in device usage, enabling quicker responses to potential security incidents. Companies that focus on creating advanced, user-friendly security solutions will find significant growth opportunities in this evolving market.
- Growing Awareness and Training Initiatives: As organizations recognize the importance of BYOD security, there is an opportunity to develop awareness and training programs for employees. Educating employees on best practices for device security and data protection can greatly reduce the risk of security breaches. Companies that offer comprehensive training solutions and resources can help organizations foster a security-conscious culture among employees. This focus on education and awareness will not only enhance overall security but also create a demand for BYOD security solutions and services.
Market Report Scope
Key Selling Points
- Comprehensive Coverage: The report comprehensively covers the analysis of products, services, types, and end users of the BYOD Security Market, providing a holistic landscape.
- Expert Analysis: The report is compiled based on the in-depth understanding of industry experts and analysts.
- Up-to-date Information: The report assures business relevance due to its coverage of recent information and data trends.
- Customization Options: This report can be customized to cater to specific client requirements and suit the business strategies aptly.
The research report on the BYOD Security Market can, therefore, help spearhead the trail of decoding and understanding the industry scenario and growth prospects. Although there can be a few valid concerns, the overall benefits of this report tend to outweigh the disadvantages.
REGIONAL FRAMEWORK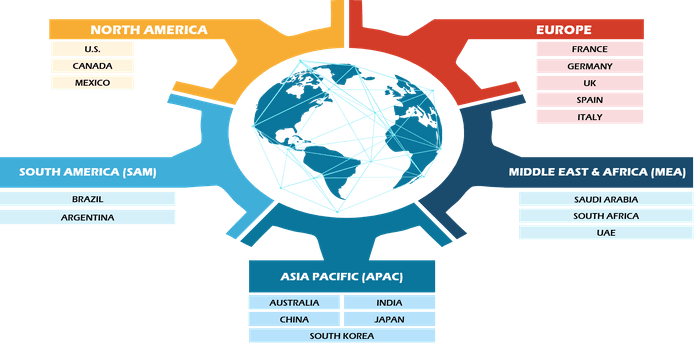
Have a question?

Naveen
Naveen will walk you through a 15-minute call to present the report’s content and answer all queries if you have any.
 Speak to Analyst
Speak to Analyst
- Sample PDF showcases the content structure and the nature of the information with qualitative and quantitative analysis.
- Request discounts available for Start-Ups & Universities
- Sample PDF showcases the content structure and the nature of the information with qualitative and quantitative analysis.
- Request discounts available for Start-Ups & Universities
Report Coverage
Revenue forecast, Company Analysis, Industry landscape, Growth factors, and Trends
Segment Covered
This text is related
to segments covered.
Regional Scope
North America, Europe, Asia Pacific, Middle East & Africa, South & Central America
Country Scope
This text is related
to country scope.
Frequently Asked Questions
Some of the customization options available based on the request are an additional 3-5 company profiles and country-specific analysis of 3-5 countries of your choice. Customizations are to be requested/discussed before making final order confirmation# as our team would review the same and check the feasibility
The report can be delivered in PDF/PPT format; we can also share excel dataset based on the request
Zero trust security model to play a significant role in the global BYOD security market in the coming years
Increasing BYOD adoption and remote working & flexibility are the major factors driving the BYOD security market
The BYOD Security Market is estimated to witness a CAGR of 14.5% from 2023 to 2031
1. INTRODUCTION
1.1. SCOPE OF THE STUDY
1.2. THE INSIGHT PARTNERS RESEARCH REPORT GUIDANCE
1.3. MARKET SEGMENTATION
1.3.1BYOD Security Market - By Device Type
1.3.2BYOD Security Market - By Solution
1.3.3BYOD Security Market - By Software
1.3.4BYOD Security Market - By Enterprise Size
1.3.5BYOD Security Market - By Region
1.3.5.1By Country
2. KEY TAKEAWAYS
3. RESEARCH METHODOLOGY
4.BYOD SECURITY MARKET LANDSCAPE
4.1.OVERVIEW
4.2.PEST ANALYSIS
4.2.1North America - Pest Analysis
4.2.2Europe - Pest Analysis
4.2.3Asia-Pacific - Pest Analysis
4.2.4Middle East and Africa - Pest Analysis
4.2.5South and Central America - Pest Analysis
4.3.ECOSYSTEM ANALYSIS
4.4.EXPERT OPINIONS
5.BYOD SECURITY MARKET - KEY MARKET DYNAMICS
5.1.KEY MARKET DRIVERS
5.2.KEY MARKET RESTRAINTS
5.3.KEY MARKET OPPORTUNITIES
5.4.FUTURE TRENDS
5.5.IMPACT ANALYSIS OF DRIVERS AND RESTRAINTS
6.BYOD SECURITY MARKET - GLOBAL MARKET ANALYSIS
6.1.BYOD SECURITY - GLOBAL MARKET OVERVIEW
6.2.BYOD SECURITY - GLOBAL MARKET AND FORECAST TO 2028
6.3.MARKET POSITIONING/MARKET SHARE
7.BYOD SECURITY MARKET - REVENUE AND FORECASTS TO 2028- DEVICE TYPE
7.1.OVERVIEW
7.2.DEVICE TYPE MARKET FORECASTS AND ANALYSIS
7.3.LAPTOP
7.3.1.Overview
7.3.2.Laptop Market Forecast and Analysis
7.4.SMARTPHONE
7.4.1.Overview
7.4.2.Smartphone Market Forecast and Analysis
7.5.TABLET
7.5.1.Overview
7.5.2.Tablet Market Forecast and Analysis
8.BYOD SECURITY MARKET - REVENUE AND FORECASTS TO 2028- SOLUTION
8.1.OVERVIEW
8.2.SOLUTION MARKET FORECASTS AND ANALYSIS
8.3.MOBILE DEVICE MANAGEMENT (MDM)
8.3.1.Overview
8.3.2.Mobile Device Management (MDM) Market Forecast and Analysis
8.4.MOBILE APPLICATION MANAGEMENT (MAM)
8.4.1.Overview
8.4.2.Mobile Application Management (MAM) Market Forecast and Analysis
8.5.MOBILE CONTENT MANAGEMENT (MCM)
8.5.1.Overview
8.5.2.Mobile Content Management (MCM) Market Forecast and Analysis
8.6.MOBILE IDENTITY MANAGEMENT (MIM)
8.6.1.Overview
8.6.2.Mobile Identity Management (MIM) Market Forecast and Analysis
9.BYOD SECURITY MARKET - REVENUE AND FORECASTS TO 2028- SOFTWARE
9.1.OVERVIEW
9.2.SOFTWARE MARKET FORECASTS AND ANALYSIS
9.3.MOBILE DATA SECURITY
9.3.1.Overview
9.3.2.Mobile Data Security Market Forecast and Analysis
9.4.MOBILE DEVICE SECURITY
9.4.1.Overview
9.4.2.Mobile Device Security Market Forecast and Analysis
9.5.NETWORK SECURITY
9.5.1.Overview
9.5.2.Network Security Market Forecast and Analysis
10.BYOD SECURITY MARKET - REVENUE AND FORECASTS TO 2028- ENTERPRISE SIZE
10.1.OVERVIEW
10.2.ENTERPRISE SIZE MARKET FORECASTS AND ANALYSIS
10.3.SMALL AND MEDIUM-SIZE ENTERPRISES
10.3.1.Overview
10.3.2.Small and Medium-Size Enterprises Market Forecast and Analysis
10.4.LARGE ENTERPRISES
10.4.1.Overview
10.4.2.Large Enterprises Market Forecast and Analysis
11.BYOD SECURITY MARKET REVENUE AND FORECASTS TO 2028- GEOGRAPHICAL ANALYSIS
11.1.NORTH AMERICA
11.1.1North America BYOD Security Market Overview
11.1.2North America BYOD Security Market Forecasts and Analysis
11.1.3North America BYOD Security Market Forecasts and Analysis - By Device Type
11.1.4North America BYOD Security Market Forecasts and Analysis - By Solution
11.1.5North America BYOD Security Market Forecasts and Analysis - By Software
11.1.6North America BYOD Security Market Forecasts and Analysis - By Enterprise Size
11.1.7North America BYOD Security Market Forecasts and Analysis - By Countries
11.1.7.1United States BYOD Security Market
11.1.7.1.1United States BYOD Security Market by Device Type
11.1.7.1.2United States BYOD Security Market by Solution
11.1.7.1.3United States BYOD Security Market by Software
11.1.7.1.4United States BYOD Security Market by Enterprise Size
11.1.7.2Canada BYOD Security Market
11.1.7.2.1Canada BYOD Security Market by Device Type
11.1.7.2.2Canada BYOD Security Market by Solution
11.1.7.2.3Canada BYOD Security Market by Software
11.1.7.2.4Canada BYOD Security Market by Enterprise Size
11.1.7.3Mexico BYOD Security Market
11.1.7.3.1Mexico BYOD Security Market by Device Type
11.1.7.3.2Mexico BYOD Security Market by Solution
11.1.7.3.3Mexico BYOD Security Market by Software
11.1.7.3.4Mexico BYOD Security Market by Enterprise Size
11.2.EUROPE
11.2.1Europe BYOD Security Market Overview
11.2.2Europe BYOD Security Market Forecasts and Analysis
11.2.3Europe BYOD Security Market Forecasts and Analysis - By Device Type
11.2.4Europe BYOD Security Market Forecasts and Analysis - By Solution
11.2.5Europe BYOD Security Market Forecasts and Analysis - By Software
11.2.6Europe BYOD Security Market Forecasts and Analysis - By Enterprise Size
11.2.7Europe BYOD Security Market Forecasts and Analysis - By Countries
11.2.7.1Germany BYOD Security Market
11.2.7.1.1Germany BYOD Security Market by Device Type
11.2.7.1.2Germany BYOD Security Market by Solution
11.2.7.1.3Germany BYOD Security Market by Software
11.2.7.1.4Germany BYOD Security Market by Enterprise Size
11.2.7.2France BYOD Security Market
11.2.7.2.1France BYOD Security Market by Device Type
11.2.7.2.2France BYOD Security Market by Solution
11.2.7.2.3France BYOD Security Market by Software
11.2.7.2.4France BYOD Security Market by Enterprise Size
11.2.7.3Italy BYOD Security Market
11.2.7.3.1Italy BYOD Security Market by Device Type
11.2.7.3.2Italy BYOD Security Market by Solution
11.2.7.3.3Italy BYOD Security Market by Software
11.2.7.3.4Italy BYOD Security Market by Enterprise Size
11.2.7.4United Kingdom BYOD Security Market
11.2.7.4.1United Kingdom BYOD Security Market by Device Type
11.2.7.4.2United Kingdom BYOD Security Market by Solution
11.2.7.4.3United Kingdom BYOD Security Market by Software
11.2.7.4.4United Kingdom BYOD Security Market by Enterprise Size
11.2.7.5Russia BYOD Security Market
11.2.7.5.1Russia BYOD Security Market by Device Type
11.2.7.5.2Russia BYOD Security Market by Solution
11.2.7.5.3Russia BYOD Security Market by Software
11.2.7.5.4Russia BYOD Security Market by Enterprise Size
11.2.7.6Rest of Europe BYOD Security Market
11.2.7.6.1Rest of Europe BYOD Security Market by Device Type
11.2.7.6.2Rest of Europe BYOD Security Market by Solution
11.2.7.6.3Rest of Europe BYOD Security Market by Software
11.2.7.6.4Rest of Europe BYOD Security Market by Enterprise Size
11.3.ASIA-PACIFIC
11.3.1Asia-Pacific BYOD Security Market Overview
11.3.2Asia-Pacific BYOD Security Market Forecasts and Analysis
11.3.3Asia-Pacific BYOD Security Market Forecasts and Analysis - By Device Type
11.3.4Asia-Pacific BYOD Security Market Forecasts and Analysis - By Solution
11.3.5Asia-Pacific BYOD Security Market Forecasts and Analysis - By Software
11.3.6Asia-Pacific BYOD Security Market Forecasts and Analysis - By Enterprise Size
11.3.7Asia-Pacific BYOD Security Market Forecasts and Analysis - By Countries
11.3.7.1Australia BYOD Security Market
11.3.7.1.1Australia BYOD Security Market by Device Type
11.3.7.1.2Australia BYOD Security Market by Solution
11.3.7.1.3Australia BYOD Security Market by Software
11.3.7.1.4Australia BYOD Security Market by Enterprise Size
11.3.7.2China BYOD Security Market
11.3.7.2.1China BYOD Security Market by Device Type
11.3.7.2.2China BYOD Security Market by Solution
11.3.7.2.3China BYOD Security Market by Software
11.3.7.2.4China BYOD Security Market by Enterprise Size
11.3.7.3India BYOD Security Market
11.3.7.3.1India BYOD Security Market by Device Type
11.3.7.3.2India BYOD Security Market by Solution
11.3.7.3.3India BYOD Security Market by Software
11.3.7.3.4India BYOD Security Market by Enterprise Size
11.3.7.4Japan BYOD Security Market
11.3.7.4.1Japan BYOD Security Market by Device Type
11.3.7.4.2Japan BYOD Security Market by Solution
11.3.7.4.3Japan BYOD Security Market by Software
11.3.7.4.4Japan BYOD Security Market by Enterprise Size
11.3.7.5South Korea BYOD Security Market
11.3.7.5.1South Korea BYOD Security Market by Device Type
11.3.7.5.2South Korea BYOD Security Market by Solution
11.3.7.5.3South Korea BYOD Security Market by Software
11.3.7.5.4South Korea BYOD Security Market by Enterprise Size
11.3.7.6Rest of Asia-Pacific BYOD Security Market
11.3.7.6.1Rest of Asia-Pacific BYOD Security Market by Device Type
11.3.7.6.2Rest of Asia-Pacific BYOD Security Market by Solution
11.3.7.6.3Rest of Asia-Pacific BYOD Security Market by Software
11.3.7.6.4Rest of Asia-Pacific BYOD Security Market by Enterprise Size
11.4.MIDDLE EAST AND AFRICA
11.4.1Middle East and Africa BYOD Security Market Overview
11.4.2Middle East and Africa BYOD Security Market Forecasts and Analysis
11.4.3Middle East and Africa BYOD Security Market Forecasts and Analysis - By Device Type
11.4.4Middle East and Africa BYOD Security Market Forecasts and Analysis - By Solution
11.4.5Middle East and Africa BYOD Security Market Forecasts and Analysis - By Software
11.4.6Middle East and Africa BYOD Security Market Forecasts and Analysis - By Enterprise Size
11.4.7Middle East and Africa BYOD Security Market Forecasts and Analysis - By Countries
11.4.7.1South Africa BYOD Security Market
11.4.7.1.1South Africa BYOD Security Market by Device Type
11.4.7.1.2South Africa BYOD Security Market by Solution
11.4.7.1.3South Africa BYOD Security Market by Software
11.4.7.1.4South Africa BYOD Security Market by Enterprise Size
11.4.7.2Saudi Arabia BYOD Security Market
11.4.7.2.1Saudi Arabia BYOD Security Market by Device Type
11.4.7.2.2Saudi Arabia BYOD Security Market by Solution
11.4.7.2.3Saudi Arabia BYOD Security Market by Software
11.4.7.2.4Saudi Arabia BYOD Security Market by Enterprise Size
11.4.7.3U.A.E BYOD Security Market
11.4.7.3.1U.A.E BYOD Security Market by Device Type
11.4.7.3.2U.A.E BYOD Security Market by Solution
11.4.7.3.3U.A.E BYOD Security Market by Software
11.4.7.3.4U.A.E BYOD Security Market by Enterprise Size
11.4.7.4Rest of Middle East and Africa BYOD Security Market
11.4.7.4.1Rest of Middle East and Africa BYOD Security Market by Device Type
11.4.7.4.2Rest of Middle East and Africa BYOD Security Market by Solution
11.4.7.4.3Rest of Middle East and Africa BYOD Security Market by Software
11.4.7.4.4Rest of Middle East and Africa BYOD Security Market by Enterprise Size
11.5.SOUTH AND CENTRAL AMERICA
11.5.1South and Central America BYOD Security Market Overview
11.5.2South and Central America BYOD Security Market Forecasts and Analysis
11.5.3South and Central America BYOD Security Market Forecasts and Analysis - By Device Type
11.5.4South and Central America BYOD Security Market Forecasts and Analysis - By Solution
11.5.5South and Central America BYOD Security Market Forecasts and Analysis - By Software
11.5.6South and Central America BYOD Security Market Forecasts and Analysis - By Enterprise Size
11.5.7South and Central America BYOD Security Market Forecasts and Analysis - By Countries
11.5.7.1Brazil BYOD Security Market
11.5.7.1.1Brazil BYOD Security Market by Device Type
11.5.7.1.2Brazil BYOD Security Market by Solution
11.5.7.1.3Brazil BYOD Security Market by Software
11.5.7.1.4Brazil BYOD Security Market by Enterprise Size
11.5.7.2Argentina BYOD Security Market
11.5.7.2.1Argentina BYOD Security Market by Device Type
11.5.7.2.2Argentina BYOD Security Market by Solution
11.5.7.2.3Argentina BYOD Security Market by Software
11.5.7.2.4Argentina BYOD Security Market by Enterprise Size
11.5.7.3Rest of South and Central America BYOD Security Market
11.5.7.3.1Rest of South and Central America BYOD Security Market by Device Type
11.5.7.3.2Rest of South and Central America BYOD Security Market by Solution
11.5.7.3.3Rest of South and Central America BYOD Security Market by Software
11.5.7.3.4Rest of South and Central America BYOD Security Market by Enterprise Size
12.INDUSTRY LANDSCAPE
12.1.MERGERS AND ACQUISITIONS
12.2.AGREEMENTS, COLLABORATIONS AND JOIN VENTURES
12.3.NEW PRODUCT LAUNCHES
12.4.EXPANSIONS AND OTHER STRATEGIC DEVELOPMENTS
13.BYOD SECURITY MARKET, KEY COMPANY PROFILES
13.1.BLACKBERRY LIMITED
13.1.1.Key Facts
13.1.2.Business Description
13.1.3.Products and Services
13.1.4.Financial Overview
13.1.5.SWOT Analysis
13.1.6.Key Developments
13.2.BROADCOM, INC.
13.2.1.Key Facts
13.2.2.Business Description
13.2.3.Products and Services
13.2.4.Financial Overview
13.2.5.SWOT Analysis
13.2.6.Key Developments
13.3.CISCO SYSTEMS, INC.
13.3.1.Key Facts
13.3.2.Business Description
13.3.3.Products and Services
13.3.4.Financial Overview
13.3.5.SWOT Analysis
13.3.6.Key Developments
13.4.CITRIX SYSTEMS, INC.
13.4.1.Key Facts
13.4.2.Business Description
13.4.3.Products and Services
13.4.4.Financial Overview
13.4.5.SWOT Analysis
13.4.6.Key Developments
13.5.IBM CORPORATION
13.5.1.Key Facts
13.5.2.Business Description
13.5.3.Products and Services
13.5.4.Financial Overview
13.5.5.SWOT Analysis
13.5.6.Key Developments
13.6.KASPERSKY LAB
13.6.1.Key Facts
13.6.2.Business Description
13.6.3.Products and Services
13.6.4.Financial Overview
13.6.5.SWOT Analysis
13.6.6.Key Developments
13.7.MOBILEIRON INC.
13.7.1.Key Facts
13.7.2.Business Description
13.7.3.Products and Services
13.7.4.Financial Overview
13.7.5.SWOT Analysis
13.7.6.Key Developments
13.8.SAP SE
13.8.1.Key Facts
13.8.2.Business Description
13.8.3.Products and Services
13.8.4.Financial Overview
13.8.5.SWOT Analysis
13.8.6.Key Developments
13.9.TREND MICRO INCORPORATED
13.9.1.Key Facts
13.9.2.Business Description
13.9.3.Products and Services
13.9.4.Financial Overview
13.9.5.SWOT Analysis
13.9.6.Key Developments
13.10.VMWARE, INC.
13.10.1.Key Facts
13.10.2.Business Description
13.10.3.Products and Services
13.10.4.Financial Overview
13.10.5.SWOT Analysis
13.10.6.Key Developments
14.APPENDIX
14.1.ABOUT THE INSIGHT PARTNERS
14.2.GLOSSARY OF TERMS
1. BlackBerry Limited
2. Broadcom, Inc.
3. Cisco Systems, Inc.
4. Citrix Systems, Inc.
5. IBM Corporation
6. Kaspersky Lab
7. MobileIron Inc.
8. SAP SE
9. Trend Micro Incorporated
10. VMware, Inc.
The Insight Partners performs research in 4 major stages: Data Collection & Secondary Research, Primary Research, Data Analysis and Data Triangulation & Final Review.
- Data Collection and Secondary Research:
As a market research and consulting firm operating from a decade, we have published many reports and advised several clients across the globe. First step for any study will start with an assessment of currently available data and insights from existing reports. Further, historical and current market information is collected from Investor Presentations, Annual Reports, SEC Filings, etc., and other information related to company’s performance and market positioning are gathered from Paid Databases (Factiva, Hoovers, and Reuters) and various other publications available in public domain.
Several associations trade associates, technical forums, institutes, societies and organizations are accessed to gain technical as well as market related insights through their publications such as research papers, blogs and press releases related to the studies are referred to get cues about the market. Further, white papers, journals, magazines, and other news articles published in the last 3 years are scrutinized and analyzed to understand the current market trends.
- Primary Research:
The primarily interview analysis comprise of data obtained from industry participants interview and answers to survey questions gathered by in-house primary team.
For primary research, interviews are conducted with industry experts/CEOs/Marketing Managers/Sales Managers/VPs/Subject Matter Experts from both demand and supply side to get a 360-degree view of the market. The primary team conducts several interviews based on the complexity of the markets to understand the various market trends and dynamics which makes research more credible and precise.
A typical research interview fulfils the following functions:
- Provides first-hand information on the market size, market trends, growth trends, competitive landscape, and outlook
- Validates and strengthens in-house secondary research findings
- Develops the analysis team’s expertise and market understanding
Primary research involves email interactions and telephone interviews for each market, category, segment, and sub-segment across geographies. The participants who typically take part in such a process include, but are not limited to:
- Industry participants: VPs, business development managers, market intelligence managers and national sales managers
- Outside experts: Valuation experts, research analysts and key opinion leaders specializing in the electronics and semiconductor industry.
Below is the breakup of our primary respondents by company, designation, and region:
Once we receive the confirmation from primary research sources or primary respondents, we finalize the base year market estimation and forecast the data as per the macroeconomic and microeconomic factors assessed during data collection.
- Data Analysis:
Once data is validated through both secondary as well as primary respondents, we finalize the market estimations by hypothesis formulation and factor analysis at regional and country level.
- 3.1 Macro-Economic Factor Analysis:
We analyse macroeconomic indicators such the gross domestic product (GDP), increase in the demand for goods and services across industries, technological advancement, regional economic growth, governmental policies, the influence of COVID-19, PEST analysis, and other aspects. This analysis aids in setting benchmarks for various nations/regions and approximating market splits. Additionally, the general trend of the aforementioned components aid in determining the market's development possibilities.
- 3.2 Country Level Data:
Various factors that are especially aligned to the country are taken into account to determine the market size for a certain area and country, including the presence of vendors, such as headquarters and offices, the country's GDP, demand patterns, and industry growth. To comprehend the market dynamics for the nation, a number of growth variables, inhibitors, application areas, and current market trends are researched. The aforementioned elements aid in determining the country's overall market's growth potential.
- 3.3 Company Profile:
The “Table of Contents” is formulated by listing and analyzing more than 25 - 30 companies operating in the market ecosystem across geographies. However, we profile only 10 companies as a standard practice in our syndicate reports. These 10 companies comprise leading, emerging, and regional players. Nonetheless, our analysis is not restricted to the 10 listed companies, we also analyze other companies present in the market to develop a holistic view and understand the prevailing trends. The “Company Profiles” section in the report covers key facts, business description, products & services, financial information, SWOT analysis, and key developments. The financial information presented is extracted from the annual reports and official documents of the publicly listed companies. Upon collecting the information for the sections of respective companies, we verify them via various primary sources and then compile the data in respective company profiles. The company level information helps us in deriving the base number as well as in forecasting the market size.
- 3.4 Developing Base Number:
Aggregation of sales statistics (2020-2022) and macro-economic factor, and other secondary and primary research insights are utilized to arrive at base number and related market shares for 2022. The data gaps are identified in this step and relevant market data is analyzed, collected from paid primary interviews or databases. On finalizing the base year market size, forecasts are developed on the basis of macro-economic, industry and market growth factors and company level analysis.
- Data Triangulation and Final Review:
The market findings and base year market size calculations are validated from supply as well as demand side. Demand side validations are based on macro-economic factor analysis and benchmarks for respective regions and countries. In case of supply side validations, revenues of major companies are estimated (in case not available) based on industry benchmark, approximate number of employees, product portfolio, and primary interviews revenues are gathered. Further revenue from target product/service segment is assessed to avoid overshooting of market statistics. In case of heavy deviations between supply and demand side values, all thes steps are repeated to achieve synchronization.
We follow an iterative model, wherein we share our research findings with Subject Matter Experts (SME’s) and Key Opinion Leaders (KOLs) until consensus view of the market is not formulated – this model negates any drastic deviation in the opinions of experts. Only validated and universally acceptable research findings are quoted in our reports.
We have important check points that we use to validate our research findings – which we call – data triangulation, where we validate the information, we generate from secondary sources with primary interviews and then we re-validate with our internal data bases and Subject matter experts. This comprehensive model enables us to deliver high quality, reliable data in shortest possible time.

 Get Free Sample For
Get Free Sample For