Confidential Computing Market Strategies and Share 2031
Confidential computing is a concept in which encrypted data can be processed in memory to limit access to ensure data in use is protected. Confidential computing is a concept promoted by the Confidential Computing Consortium, which is a group of organizations that wants to build tools supporting the protection of data. This concept is especially suitable for public clouds.
MARKET DYNAMICS
Increasing number of cyber threats is one of the major factors driving the growth of the confidential computing market. Moreover, confidential computing protects data during processing, and when combined with storage and network encryption with exclusive control of encryption keys, provides end-to-end data security in the cloud, this is another factor anticipated to boost the growth of the market.
MARKET SCOPE
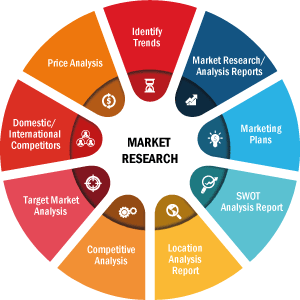
The "Global Confidential Computing Market Analysis to 2031" is a specialized and in-depth study of the confidential computing market with a special focus on the global market trend analysis. The report aims to provide an overview of confidential computing market with detailed market segmentation by deployment type, components, application. The global confidential computing market expected to witness high growth during the forecast period. The report provides key statistics on the market status of the leading confidential computing market player and offers key trends and opportunities in the confidential computing market.
MARKET SEGMENTATION
The global confidential computing market is segmented on the basis of deployment type, components, application. On the basis of deployment type, market is segmented as cloud-based, on-premises. On the basis of component, market is segmented as hardware, software. On the basis of application, market is segmented as data security, secure enclaves, pellucidity between users, others
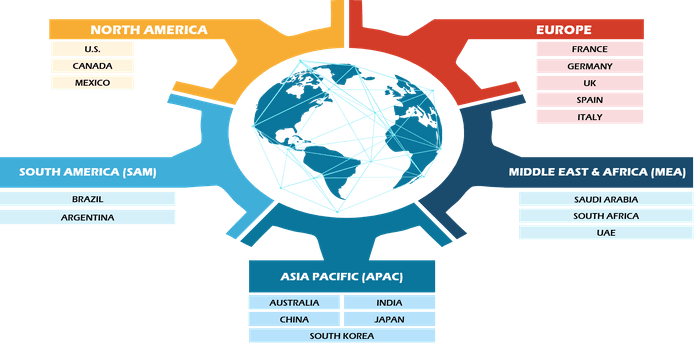
REGIONAL FRAMEWORK
The report provides a detailed overview of the industry including both qualitative and quantitative information. It provides overview and forecast of the global confidential computing market based on various segments. It also provides market size and forecast estimates from year 2021 to 2031 with respect to five major regions, namely; North America, Europe, Asia-Pacific (APAC), Middle East and Africa (MEA) and South America. The confidential computing market by each region is later sub-segmented by respective countries and segments. The report covers analysis and forecast of 18 countries globally along with current trend and opportunities prevailing in the region.
The report analyzes factors affecting confidential computing market from both demand and supply side and further evaluates market dynamics effecting the market during the forecast period i.e., drivers, restraints, opportunities, and future trend. The report also provides exhaustive PEST analysis for all five regions namely; North America, Europe, APAC, MEA and South America after evaluating political, economic, social and technological factors effecting the confidential computing market in these regions.
Have a question?

Naveen
Naveen will walk you through a 15-minute call to present the report’s content and answer all queries if you have any.
 Speak to Analyst
Speak to Analyst
- Sample PDF showcases the content structure and the nature of the information with qualitative and quantitative analysis.
- Request discounts available for Start-Ups & Universities
The report provides a detailed overview of the industry including both qualitative and quantitative information. It provides overview and forecast of the global confidential computing market based on various segments. It also provides market size and forecast estimates from year 2021 to 2031 with respect to five major regions, namely; North America, Europe, Asia-Pacific (APAC), Middle East and Africa (MEA) and South America. The confidential computing market by each region is later sub-segmented by respective countries and segments. The report covers analysis and forecast of 18 countries globally along with current trend and opportunities prevailing in the region.
The report analyzes factors affecting confidential computing market from both demand and supply side and further evaluates market dynamics effecting the market during the forecast period i.e., drivers, restraints, opportunities, and future trend. The report also provides exhaustive PEST analysis for all five regions namely; North America, Europe, APAC, MEA and South America after evaluating political, economic, social and technological factors effecting the confidential computing market in these regions.
MARKET PLAYERS
The reports cover key developments in the confidential computing market organic and inorganic growth strategies. Various companies are focusing on organic growth strategies such as product launches, product approvals and others such as patents and events. Inorganic growth strategies activities witnessed in the market were acquisitions, and partnership & collaborations. These activities have paved way for expansion of business and customer base of market players. The market players from confidential computing market are anticipated to lucrative growth opportunities in the future with the rising demand for confidential computing market. Below mentioned is the list of few companies engaged in the confidential computing market.
The report also includes the profiles of key confidential computing market companies along with their SWOT analysis and market strategies. In addition, the report focuses on leading industry players with information such as company profiles, components and services offered, financial information of last 3 years, key development in past five years.
- Fortanix
- HUB Security
- Google Cloud
- IBM
- Intel Corporation
- Microsoft
- dq technologies AG (Decentriq)
- Advanced Micro Devices, Inc
- Applied Blockchain
- Edgeless Systems
The Insight Partner's dedicated research and analysis team consist of experienced professionals with advanced statistical expertise and offer various customization options in the existing study.
- Sample PDF showcases the content structure and the nature of the information with qualitative and quantitative analysis.
- Request discounts available for Start-Ups & Universities
Report Coverage
Revenue forecast, Company Analysis, Industry landscape, Growth factors, and Trends
Segment Covered
This text is related
to segments covered.
Regional Scope
North America, Europe, Asia Pacific, Middle East & Africa, South & Central America
Country Scope
This text is related
to country scope.
1.INTRODUCTION
1.1.SCOPE OF THE STUDY
1.2.THE INSIGHT PARTNERS RESEARCH REPORT GUIDANCE
1.3.MARKET SEGMENTATION
1.3.1Confidential Computing Market - By Deployment Type
1.3.2Confidential Computing Market - By Components
1.3.3Confidential Computing Market - By Application
1.3.4Confidential Computing Market - By Region
1.3.4.1By Country
2.KEY TAKEAWAYS
3.RESEARCH METHODOLOGY
4.CONFIDENTIAL COMPUTING MARKET LANDSCAPE
4.1.OVERVIEW
4.2.PORTER'S FIVE FORCES ANALYSIS
4.2.1Bargaining Power of Buyers
4.2.1Bargaining Power of Suppliers
4.2.1Threat of Substitute
4.2.1Threat of New Entrants
4.2.1Competitive Rivalry
4.3.ECOSYSTEM ANALYSIS
4.4.EXPERT OPINIONS
5.CONFIDENTIAL COMPUTING MARKET - KEY MARKET DYNAMICS
5.1.KEY MARKET DRIVERS
5.2.KEY MARKET RESTRAINTS
5.3.KEY MARKET OPPORTUNITIES
5.4.FUTURE TRENDS
5.5.IMPACT ANALYSIS OF DRIVERS AND RESTRAINTS
6.CONFIDENTIAL COMPUTING MARKET - GLOBAL MARKET ANALYSIS
6.1.CONFIDENTIAL COMPUTING - GLOBAL MARKET OVERVIEW
6.2.CONFIDENTIAL COMPUTING - GLOBAL MARKET AND FORECAST TO 2028
6.3.MARKET POSITIONING/MARKET SHARE
7.CONFIDENTIAL COMPUTING MARKET - REVENUE AND FORECASTS TO 2028 " DEPLOYMENT TYPE
7.1.OVERVIEW
7.2.DEPLOYMENT TYPE MARKET FORECASTS AND ANALYSIS
7.3.CLOUD-BASED
7.3.1.Overview
7.3.2.Cloud-Based Market Forecast and Analysis
7.4.ON-PREMISES
7.4.1.Overview
7.4.2.On-Premises Market Forecast and Analysis
8.CONFIDENTIAL COMPUTING MARKET - REVENUE AND FORECASTS TO 2028 " COMPONENTS
8.1.OVERVIEW
8.2.COMPONENTS MARKET FORECASTS AND ANALYSIS
8.3.HARDWARE
8.3.1.Overview
8.3.2.Hardware Market Forecast and Analysis
8.4.SOFTWARE
8.4.1.Overview
8.4.2.Software Market Forecast and Analysis
9.CONFIDENTIAL COMPUTING MARKET - REVENUE AND FORECASTS TO 2028 " APPLICATION
9.1.OVERVIEW
9.2.APPLICATION MARKET FORECASTS AND ANALYSIS
9.3.DATA SECURITY
9.3.1.Overview
9.3.2.Data Security Market Forecast and Analysis
9.4.SECURE ENCLAVES
9.4.1.Overview
9.4.2.Secure Enclaves Market Forecast and Analysis
9.5.PELLUCIDITY BETWEEN USERS
9.5.1.Overview
9.5.2.Pellucidity Between Users Market Forecast and Analysis
9.6.OTHERS
9.6.1.Overview
9.6.2.Others Market Forecast and Analysis
10.CONFIDENTIAL COMPUTING MARKET REVENUE AND FORECASTS TO 2028 " GEOGRAPHICAL ANALYSIS
10.1.NORTH AMERICA
10.1.1North America Confidential Computing Market Overview
10.1.2North America Confidential Computing Market Forecasts and Analysis
10.1.3North America Confidential Computing Market Forecasts and Analysis - By Deployment Type
10.1.4North America Confidential Computing Market Forecasts and Analysis - By Components
10.1.5North America Confidential Computing Market Forecasts and Analysis - By Application
10.1.6North America Confidential Computing Market Forecasts and Analysis - By Countries
10.1.6.1United States Confidential Computing Market
10.1.6.1.1United States Confidential Computing Market by Deployment Type
10.1.6.1.2United States Confidential Computing Market by Components
10.1.6.1.3United States Confidential Computing Market by Application
10.1.6.2Canada Confidential Computing Market
10.1.6.2.1Canada Confidential Computing Market by Deployment Type
10.1.6.2.2Canada Confidential Computing Market by Components
10.1.6.2.3Canada Confidential Computing Market by Application
10.1.6.3Mexico Confidential Computing Market
10.1.6.3.1Mexico Confidential Computing Market by Deployment Type
10.1.6.3.2Mexico Confidential Computing Market by Components
10.1.6.3.3Mexico Confidential Computing Market by Application
10.2.EUROPE
10.2.1Europe Confidential Computing Market Overview
10.2.2Europe Confidential Computing Market Forecasts and Analysis
10.2.3Europe Confidential Computing Market Forecasts and Analysis - By Deployment Type
10.2.4Europe Confidential Computing Market Forecasts and Analysis - By Components
10.2.5Europe Confidential Computing Market Forecasts and Analysis - By Application
10.2.6Europe Confidential Computing Market Forecasts and Analysis - By Countries
10.2.6.1Germany Confidential Computing Market
10.2.6.1.1Germany Confidential Computing Market by Deployment Type
10.2.6.1.2Germany Confidential Computing Market by Components
10.2.6.1.3Germany Confidential Computing Market by Application
10.2.6.2France Confidential Computing Market
10.2.6.2.1France Confidential Computing Market by Deployment Type
10.2.6.2.2France Confidential Computing Market by Components
10.2.6.2.3France Confidential Computing Market by Application
10.2.6.3Italy Confidential Computing Market
10.2.6.3.1Italy Confidential Computing Market by Deployment Type
10.2.6.3.2Italy Confidential Computing Market by Components
10.2.6.3.3Italy Confidential Computing Market by Application
10.2.6.4United Kingdom Confidential Computing Market
10.2.6.4.1United Kingdom Confidential Computing Market by Deployment Type
10.2.6.4.2United Kingdom Confidential Computing Market by Components
10.2.6.4.3United Kingdom Confidential Computing Market by Application
10.2.6.5Russia Confidential Computing Market
10.2.6.5.1Russia Confidential Computing Market by Deployment Type
10.2.6.5.2Russia Confidential Computing Market by Components
10.2.6.5.3Russia Confidential Computing Market by Application
10.2.6.6Rest of Europe Confidential Computing Market
10.2.6.6.1Rest of Europe Confidential Computing Market by Deployment Type
10.2.6.6.2Rest of Europe Confidential Computing Market by Components
10.2.6.6.3Rest of Europe Confidential Computing Market by Application
10.3.ASIA-PACIFIC
10.3.1Asia-Pacific Confidential Computing Market Overview
10.3.2Asia-Pacific Confidential Computing Market Forecasts and Analysis
10.3.3Asia-Pacific Confidential Computing Market Forecasts and Analysis - By Deployment Type
10.3.4Asia-Pacific Confidential Computing Market Forecasts and Analysis - By Components
10.3.5Asia-Pacific Confidential Computing Market Forecasts and Analysis - By Application
10.3.6Asia-Pacific Confidential Computing Market Forecasts and Analysis - By Countries
10.3.6.1Australia Confidential Computing Market
10.3.6.1.1Australia Confidential Computing Market by Deployment Type
10.3.6.1.2Australia Confidential Computing Market by Components
10.3.6.1.3Australia Confidential Computing Market by Application
10.3.6.2China Confidential Computing Market
10.3.6.2.1China Confidential Computing Market by Deployment Type
10.3.6.2.2China Confidential Computing Market by Components
10.3.6.2.3China Confidential Computing Market by Application
10.3.6.3India Confidential Computing Market
10.3.6.3.1India Confidential Computing Market by Deployment Type
10.3.6.3.2India Confidential Computing Market by Components
10.3.6.3.3India Confidential Computing Market by Application
10.3.6.4Japan Confidential Computing Market
10.3.6.4.1Japan Confidential Computing Market by Deployment Type
10.3.6.4.2Japan Confidential Computing Market by Components
10.3.6.4.3Japan Confidential Computing Market by Application
10.3.6.5South Korea Confidential Computing Market
10.3.6.5.1South Korea Confidential Computing Market by Deployment Type
10.3.6.5.2South Korea Confidential Computing Market by Components
10.3.6.5.3South Korea Confidential Computing Market by Application
10.3.6.6Rest of Asia-Pacific Confidential Computing Market
10.3.6.6.1Rest of Asia-Pacific Confidential Computing Market by Deployment Type
10.3.6.6.2Rest of Asia-Pacific Confidential Computing Market by Components
10.3.6.6.3Rest of Asia-Pacific Confidential Computing Market by Application
11.INDUSTRY LANDSCAPE
11.1.MERGERS AND ACQUISITIONS
11.2.AGREEMENTS, COLLABORATIONS AND JOIN VENTURES
11.3.NEW PRODUCT LAUNCHES
11.4.EXPANSIONS AND OTHER STRATEGIC DEVELOPMENTS
12.CONFIDENTIAL COMPUTING MARKET, KEY COMPANY PROFILES
12.1.FORTANIX
12.1.1.Key Facts
12.1.2.Business Description
12.1.3.Products and Services
12.1.4.Financial Overview
12.1.5.SWOT Analysis
12.1.6.Key Developments
12.2.HUB SECURITY
12.2.1.Key Facts
12.2.2.Business Description
12.2.3.Products and Services
12.2.4.Financial Overview
12.2.5.SWOT Analysis
12.2.6.Key Developments
12.3.GOOGLE CLOUD
12.3.1.Key Facts
12.3.2.Business Description
12.3.3.Products and Services
12.3.4.Financial Overview
12.3.5.SWOT Analysis
12.3.6.Key Developments
12.4.IBM
12.4.1.Key Facts
12.4.2.Business Description
12.4.3.Products and Services
12.4.4.Financial Overview
12.4.5.SWOT Analysis
12.4.6.Key Developments
12.5.INTEL CORPORATION
12.5.1.Key Facts
12.5.2.Business Description
12.5.3.Products and Services
12.5.4.Financial Overview
12.5.5.SWOT Analysis
12.5.6.Key Developments
12.6.MICROSOFT
12.6.1.Key Facts
12.6.2.Business Description
12.6.3.Products and Services
12.6.4.Financial Overview
12.6.5.SWOT Analysis
12.6.6.Key Developments
12.7.DQ TECHNOLOGIES AG (DECENTRIQ)
12.7.1.Key Facts
12.7.2.Business Description
12.7.3.Products and Services
12.7.4.Financial Overview
12.7.5.SWOT Analysis
12.7.6.Key Developments
12.8.ADVANCED MICRO DEVICES, INC
12.8.1.Key Facts
12.8.2.Business Description
12.8.3.Products and Services
12.8.4.Financial Overview
12.8.5.SWOT Analysis
12.8.6.Key Developments
12.9.APPLIED BLOCKCHAIN
12.9.1.Key Facts
12.9.2.Business Description
12.9.3.Products and Services
12.9.4.Financial Overview
12.9.5.SWOT Analysis
12.9.6.Key Developments
12.10.EDGELESS SYSTEMS
12.10.1.Key Facts
12.10.2.Business Description
12.10.3.Products and Services
12.10.4.Financial Overview
12.10.5.SWOT Analysis
12.10.6.Key Developments
13.APPENDIX
13.1.ABOUT THE INSIGHT PARTNERS
13.2.GLOSSARY OF TERMS
1. Fortanix
2. HUB Security
3. Google Cloud
4. IBM
5. Intel Corporation
6. Microsoft
7. dq technologies AG (Decentriq)
8. Advanced Micro Devices, Inc
9. Applied Blockchain
10. Edgeless Systems
The Insight Partners performs research in 4 major stages: Data Collection & Secondary Research, Primary Research, Data Analysis and Data Triangulation & Final Review.
- Data Collection and Secondary Research:
As a market research and consulting firm operating from a decade, we have published many reports and advised several clients across the globe. First step for any study will start with an assessment of currently available data and insights from existing reports. Further, historical and current market information is collected from Investor Presentations, Annual Reports, SEC Filings, etc., and other information related to company’s performance and market positioning are gathered from Paid Databases (Factiva, Hoovers, and Reuters) and various other publications available in public domain.
Several associations trade associates, technical forums, institutes, societies and organizations are accessed to gain technical as well as market related insights through their publications such as research papers, blogs and press releases related to the studies are referred to get cues about the market. Further, white papers, journals, magazines, and other news articles published in the last 3 years are scrutinized and analyzed to understand the current market trends.
- Primary Research:
The primarily interview analysis comprise of data obtained from industry participants interview and answers to survey questions gathered by in-house primary team.
For primary research, interviews are conducted with industry experts/CEOs/Marketing Managers/Sales Managers/VPs/Subject Matter Experts from both demand and supply side to get a 360-degree view of the market. The primary team conducts several interviews based on the complexity of the markets to understand the various market trends and dynamics which makes research more credible and precise.
A typical research interview fulfils the following functions:
- Provides first-hand information on the market size, market trends, growth trends, competitive landscape, and outlook
- Validates and strengthens in-house secondary research findings
- Develops the analysis team’s expertise and market understanding
Primary research involves email interactions and telephone interviews for each market, category, segment, and sub-segment across geographies. The participants who typically take part in such a process include, but are not limited to:
- Industry participants: VPs, business development managers, market intelligence managers and national sales managers
- Outside experts: Valuation experts, research analysts and key opinion leaders specializing in the electronics and semiconductor industry.
Below is the breakup of our primary respondents by company, designation, and region:
Once we receive the confirmation from primary research sources or primary respondents, we finalize the base year market estimation and forecast the data as per the macroeconomic and microeconomic factors assessed during data collection.
- Data Analysis:
Once data is validated through both secondary as well as primary respondents, we finalize the market estimations by hypothesis formulation and factor analysis at regional and country level.
- 3.1 Macro-Economic Factor Analysis:
We analyse macroeconomic indicators such the gross domestic product (GDP), increase in the demand for goods and services across industries, technological advancement, regional economic growth, governmental policies, the influence of COVID-19, PEST analysis, and other aspects. This analysis aids in setting benchmarks for various nations/regions and approximating market splits. Additionally, the general trend of the aforementioned components aid in determining the market's development possibilities.
- 3.2 Country Level Data:
Various factors that are especially aligned to the country are taken into account to determine the market size for a certain area and country, including the presence of vendors, such as headquarters and offices, the country's GDP, demand patterns, and industry growth. To comprehend the market dynamics for the nation, a number of growth variables, inhibitors, application areas, and current market trends are researched. The aforementioned elements aid in determining the country's overall market's growth potential.
- 3.3 Company Profile:
The “Table of Contents” is formulated by listing and analyzing more than 25 - 30 companies operating in the market ecosystem across geographies. However, we profile only 10 companies as a standard practice in our syndicate reports. These 10 companies comprise leading, emerging, and regional players. Nonetheless, our analysis is not restricted to the 10 listed companies, we also analyze other companies present in the market to develop a holistic view and understand the prevailing trends. The “Company Profiles” section in the report covers key facts, business description, products & services, financial information, SWOT analysis, and key developments. The financial information presented is extracted from the annual reports and official documents of the publicly listed companies. Upon collecting the information for the sections of respective companies, we verify them via various primary sources and then compile the data in respective company profiles. The company level information helps us in deriving the base number as well as in forecasting the market size.
- 3.4 Developing Base Number:
Aggregation of sales statistics (2020-2022) and macro-economic factor, and other secondary and primary research insights are utilized to arrive at base number and related market shares for 2022. The data gaps are identified in this step and relevant market data is analyzed, collected from paid primary interviews or databases. On finalizing the base year market size, forecasts are developed on the basis of macro-economic, industry and market growth factors and company level analysis.
- Data Triangulation and Final Review:
The market findings and base year market size calculations are validated from supply as well as demand side. Demand side validations are based on macro-economic factor analysis and benchmarks for respective regions and countries. In case of supply side validations, revenues of major companies are estimated (in case not available) based on industry benchmark, approximate number of employees, product portfolio, and primary interviews revenues are gathered. Further revenue from target product/service segment is assessed to avoid overshooting of market statistics. In case of heavy deviations between supply and demand side values, all thes steps are repeated to achieve synchronization.
We follow an iterative model, wherein we share our research findings with Subject Matter Experts (SME’s) and Key Opinion Leaders (KOLs) until consensus view of the market is not formulated – this model negates any drastic deviation in the opinions of experts. Only validated and universally acceptable research findings are quoted in our reports.
We have important check points that we use to validate our research findings – which we call – data triangulation, where we validate the information, we generate from secondary sources with primary interviews and then we re-validate with our internal data bases and Subject matter experts. This comprehensive model enables us to deliver high quality, reliable data in shortest possible time.

 Get Free Sample For
Get Free Sample For